2FA the multi-factor authentication

Securing your digital identity is one of the most important things in today’s world. Username and password are a concept from the early days. Most applications require user 1 named admin or root. So 50% of the credentials are known. And guess what? This user has the role of an administrator.
The time of post-its is over
In the past, we all used the same (perhaps complex) password for all of our internet accounts. Sometimes we used a yellow post-it on our monitor to remind us. Later, we used password stores to have one password (!) per app/platform.
Have you ever heard of attack vectors where someone owned your email account and clicked “reset password” in an app/website? Oops.
Nowadays, we need more security. This is where 2FA comes into play. Username + password + one more factor. 2FA = two-factor authentication.
Yes, it is complicated. But it is necessary!
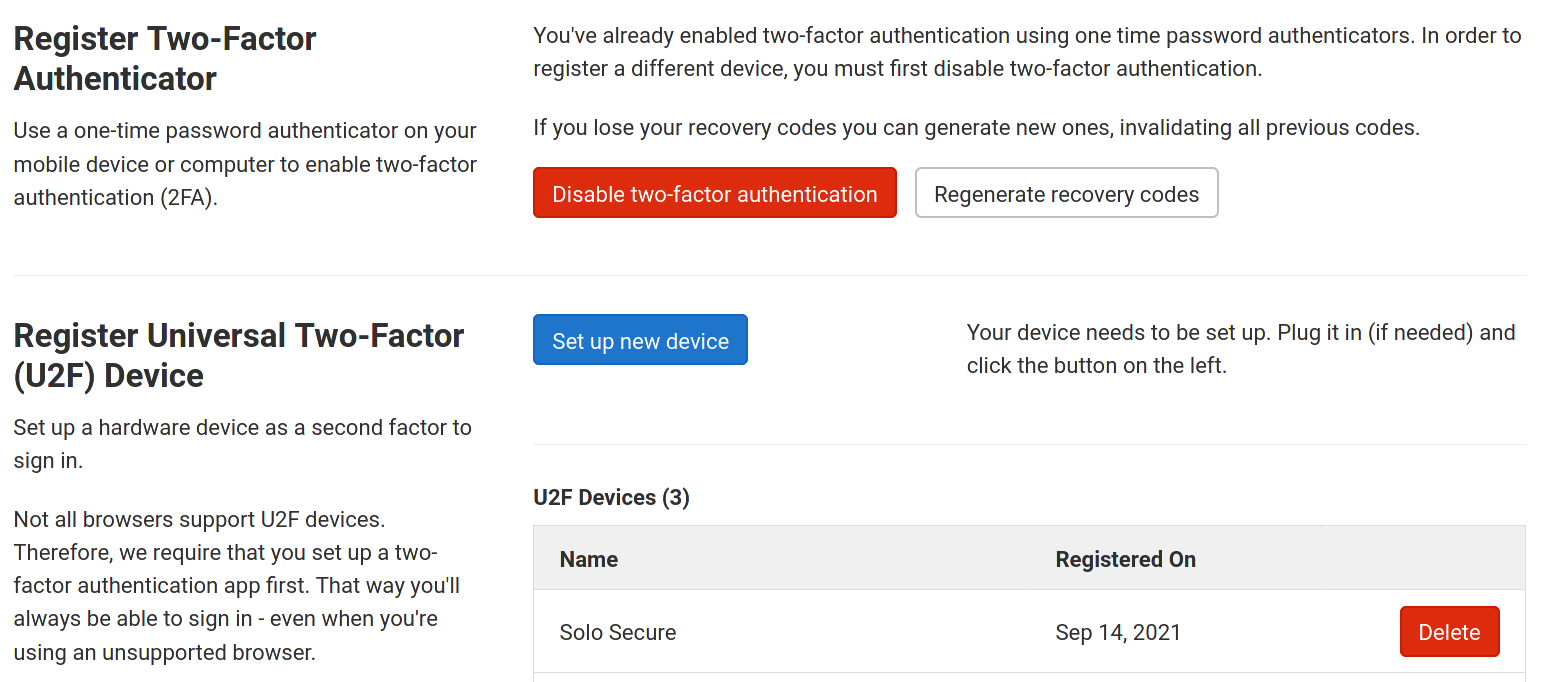
The second factor can be an app or a piece of hardware. Take a look at your beloved online service or app and search your profile settings for something called 2FA or security or similar terms. There you will often find an add 2FA button. In the case of Gitlab, you can add more than one device to your account. This is perfect because it allows you to register an additional device and keep it in your bank safe.
If you trust open source software, you should try SoloKeys. Their products are open in software and hardware.
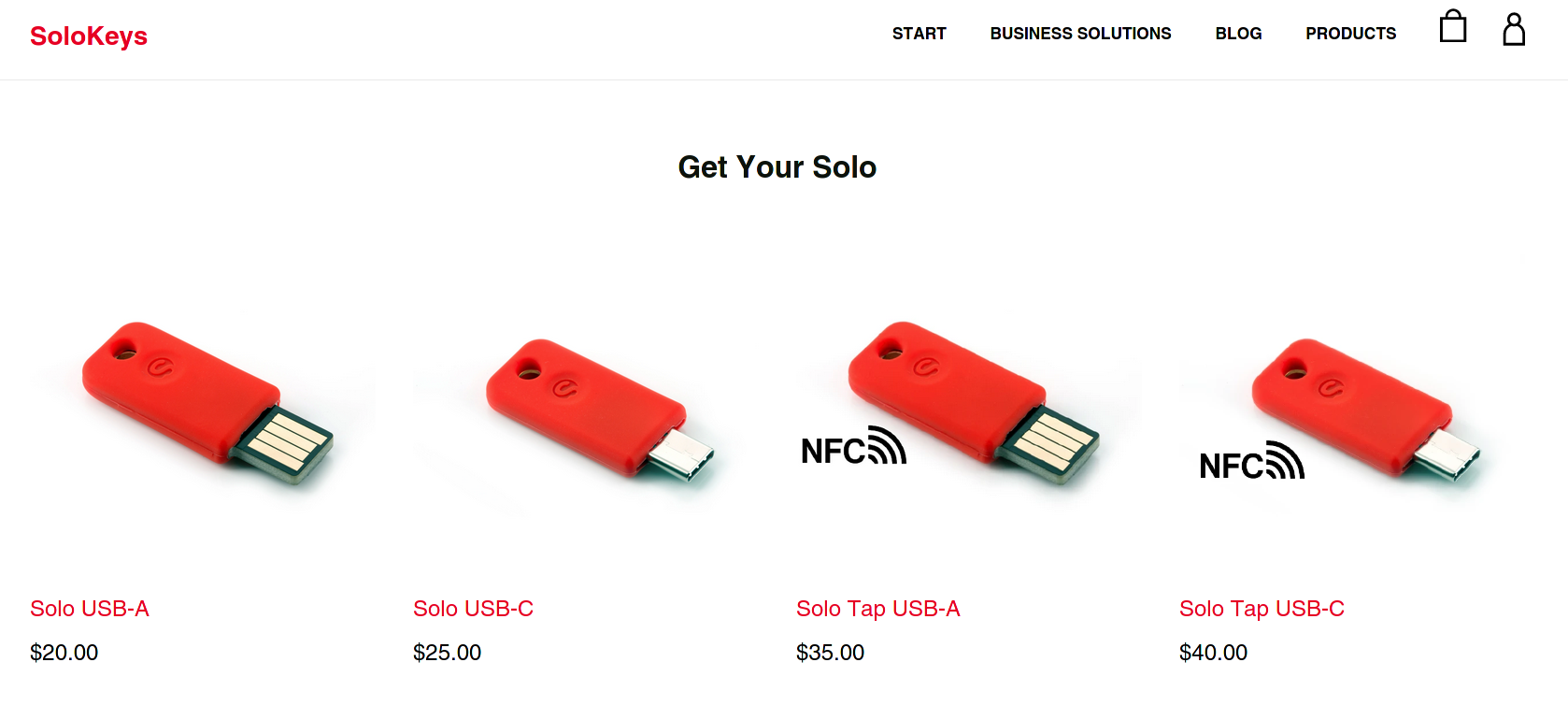
Most current browsers have hardware key support enabled. If you are using an outdated version of your operating system and perhaps an old browser version, it is possible that the hardware solution will not work.
FreeOTP
Instead of hardware, you can also use an authentication app. Google offers Google Authenticator for this purpose. However, the right app for open source enthusiasts is FreeOTP, which is also available in the f-droid store.
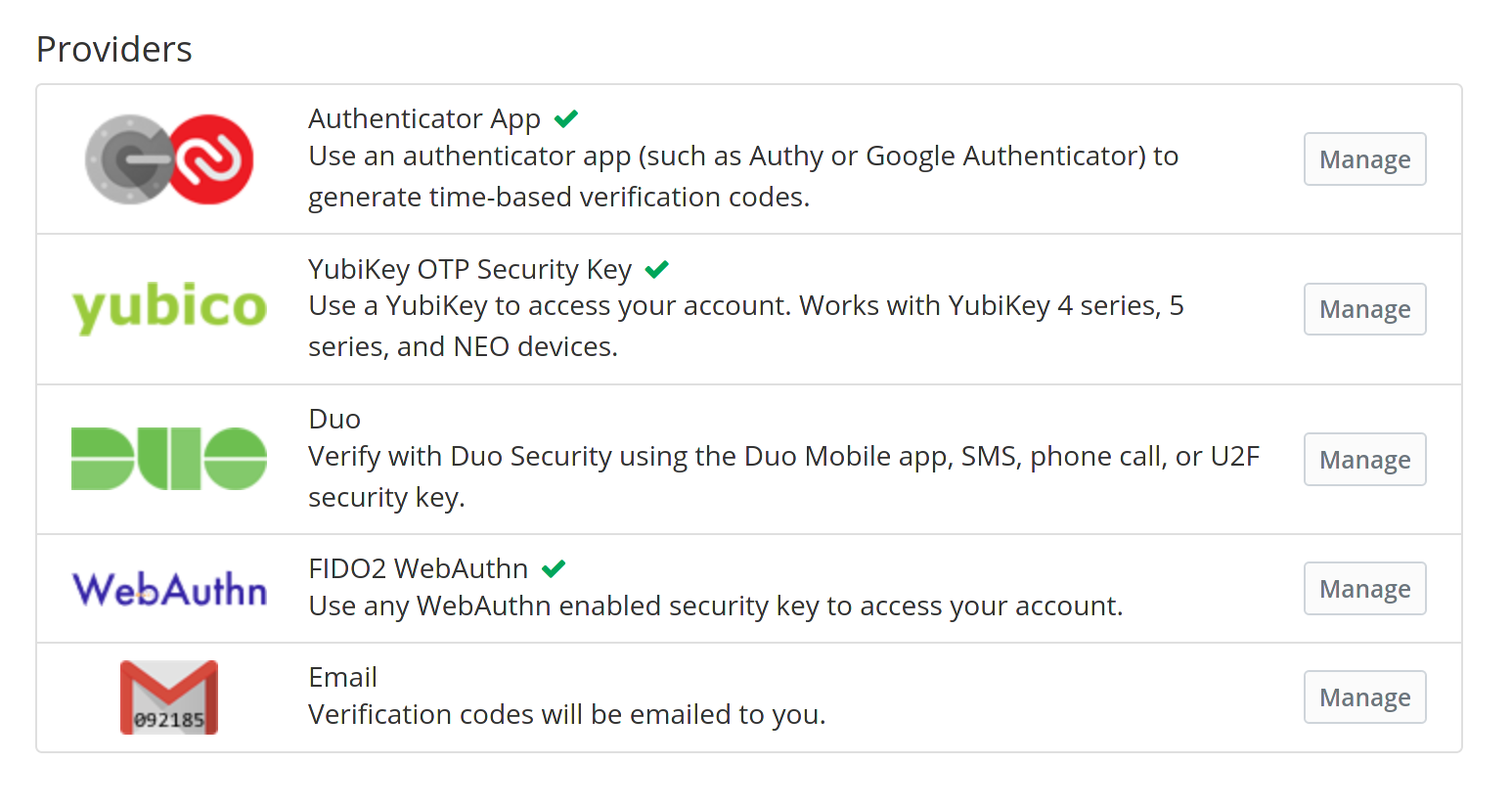
And sometimes a service or app offers different options. Here is a screenshot of vaultwarden offering Authenticator App, YubiKey, Duo, WebAuthn and Email as different second factors.
The new default
Yes, it is time-consuming. One more step. Instead of entering your username and password and clicking Sign In, you definitely need to take one more step. The service will ask you for your hardware key or TOTP token. Good if you have your key or smartphone with you. Bad for any hacker who knows your username and password but has no second factor.
Cloudron & 2FA
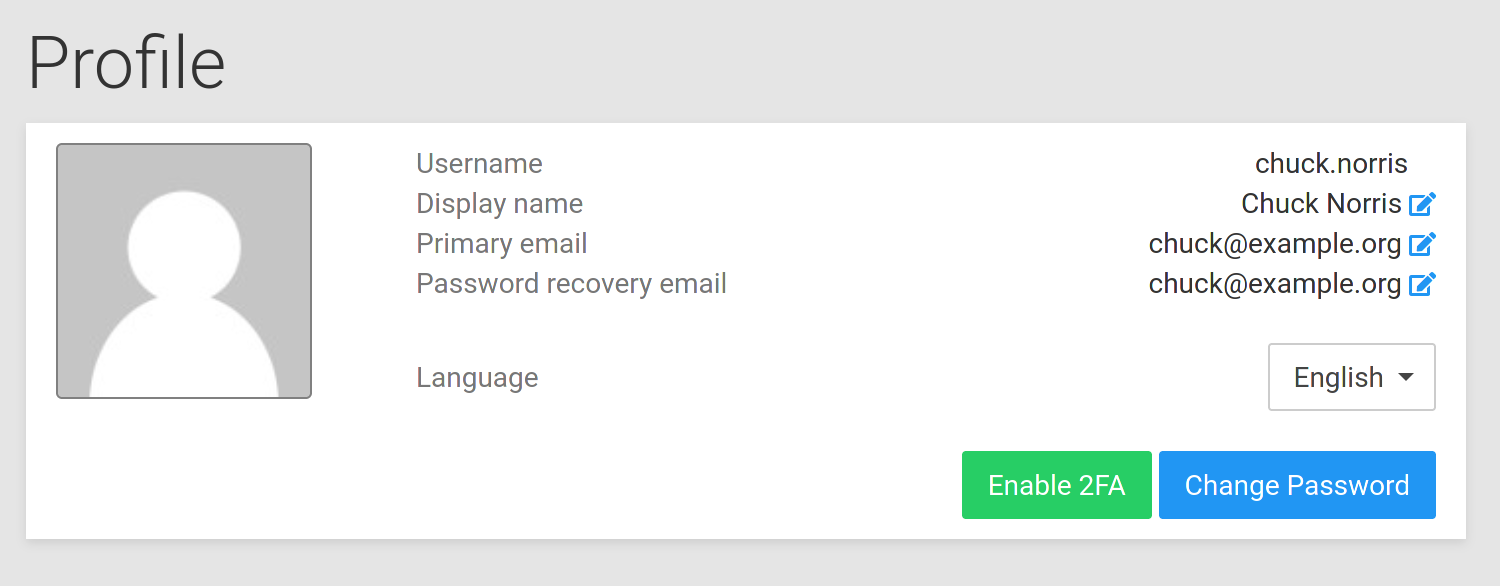
To enable 2FA for your Cloudron user account, go to the profile and click Enable 2FA.
Open your FreeOTP app and scan the barcode. Submit the generated token from the app in the dialog and click Enable.
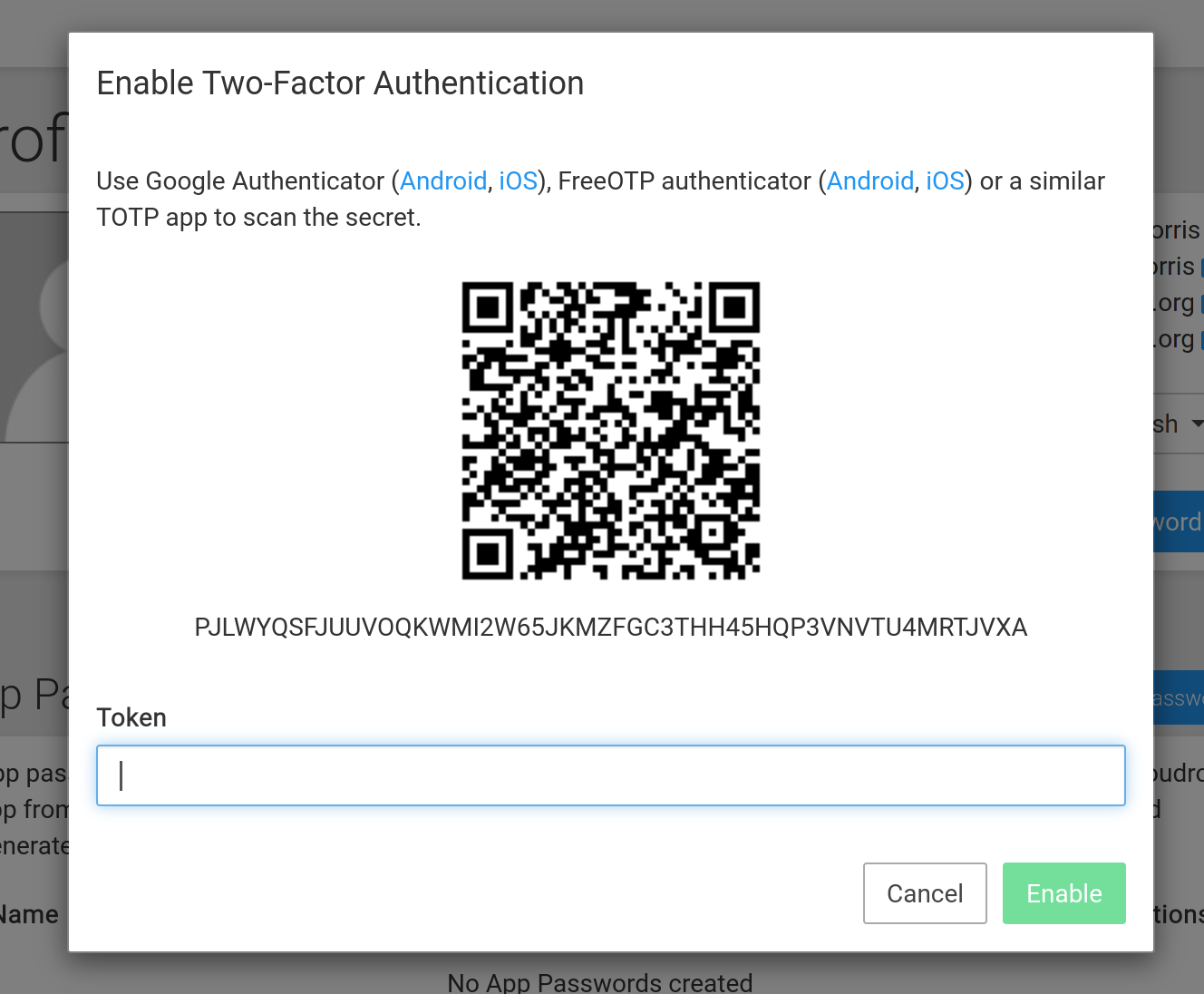
Congratulations! Your Cloudron user account is 2FA-enabled.
But beware: the 2FA you just enabled is only valid for Cloudron Dashboard. Check each app to see if it supports 2FA.
Links
Cloudron
https://www.cloudron.io/get.html
https://forum.cloudron.io/category/4/support
https://docs.cloudron.io/security/#2fa
